Want to pass Cisco 200-125 dumps exam immediately? Enjoy free CCNA Routing and Switching 200-125 dumps including entire books and also preview chapters from leading publishers. The CCNA Cisco Certified Network Associate CCNA (v3.0) (200-125 CCNA) exam is a 90 Minutes (60 – 70 questions) assessment in pass4itsure that is associated with the CCNA Routing and Switching certification. Discount Cisco 200-125 dumps CCNA exam questions and answers material try free Youtube study will be more popular. “CCNA Cisco Certified Network Associate CCNA (v3.0)” is the exam name of Pass4itsure Cisco 200-125 dumps test which designed to help candidates prepare for and pass the Cisco 200-125 exam. Read the very best Testimonies from our individuals. Some people have provided a good evaluation to the book. Immediate download totally free CCNA Routing and Switching https://www.pass4itsure.com/200-125.html dumps and get the collections of other popular e-books.
[100% Pass Guarantee Cisco 200-125 Dumps From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWT2VSaUVoODRKR1k
[100% Pass Guarantee Cisco 210-060 Dumps From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWNmlXYjFDT0t3UWc
★Pass4itsure Latest and Most Accurate Cisco 200-125 Dumps Exam Q&As(28-50)★
QUESTION 28
What are two benefits of private IPv4 IP addresses? (Choose two.)
A. They are routed the same as public IP addresses.
B. They are less costly than public IP addresses.
C. They can be assigned to devices without Internet connections.
D. They eliminate the necessity for NAT policies.
E. They eliminate duplicate IP conflicts.
200-125 exam Correct Answer: BC
QUESTION 29
Which statement about slow inter VLAN forwarding is true?
A. The VLAN is experiencing slowness in the point-to-point collisionless connection.
B. The VLANs are experiencing slowness because multiple devices are connected to the same hub.
C. The local VLAN is working normally, but traffic to the alternate VLAN is forwarded slower than expected.
D. The entire VLAN is experiencing slowness.
E. The VLANs are experiencing slowness due to a duplex mismatch.
Correct Answer: E
QUESTION 30
which two steps must you perform to enbale router-on-stick on a switch ?(choose two)
A. connect the router to a trunk port
B. config the subint number exactly the same as the matching VLAN
C. config full duplex
D. cofigure an ip route to the vlan destn net
E. assign the access port to the vlan
200-125 dumps Correct Answer: AB
QUESTION 31
Which two tasks does the Dynamic Host Configuration Protocol perform? (Choose two.)
A. Set the IP gateway to be used by the network.
B. Perform host discovery used DHCPDISCOVER message.
C. Configure IP address parameters from DHCP server to a host.
D. Provide an easy management of layer 3 devices.
E. Monitor IP performance using the DHCP server.
F. Assign and renew IP address from the default pool.
Correct Answer: CF
QUESTION 32
Scenario:
Refer to the topology. Your company has decided to connect the main office with three other remote branch offices using point-to-point serial links. You are required to troubleshoot and resolve OSPF neighbor adjacency issues between the main office and the routers located in the remote branch offices.
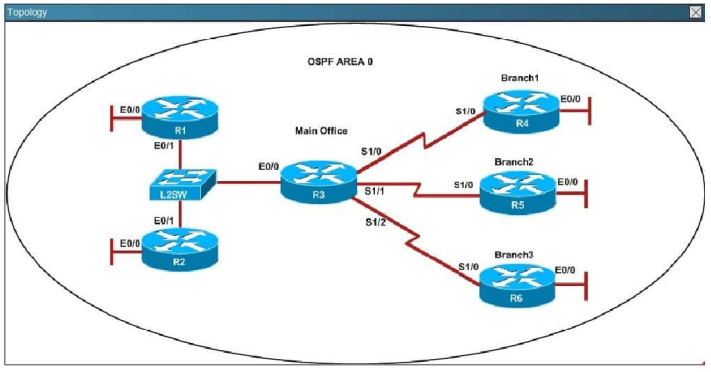
An OSPF neighbor adjacency is not formed between R3 in the main office and R4 in the Branch1 office. What is causing the problem?
A. There is an area ID mismatch.
B. There is a Layer 2 issue; an encapsulation mismatch on serial links.
C. There is an OSPF hello and dead interval mismatch.
D. The R3 router ID is configured on R4.
200-125 pdf Correct Answer: A
QUESTION 33
which three technical services support cloud computing ?
A. network-monitored power sources
B. layer 3 network routing
C. ip localization
D. redundant connections
E. VPN connectivity
F. extended SAN services
Correct Answer: CDF
QUESTION 34
Which component of the routing table ranks routing protocols according to their preferences?
A. administrative distance
B. next hop
C. metric
D. routing protocol code
200-125 vce Correct Answer: A
QUESTION 35
Which command can you execute to set the user inactivity timer to 10 seconds?
A. SW1(config-line)#exec-timeout 0 10
B. SW1(config-line)#exec-timeout 10
C. SW1(config-line)#absolute-timeout 0 10
D. SW1(config-line)#absolute-timeout 10
Correct Answer: A
QUESTION 36
Which value is used to determine the active router in an HSRP default configuration?
A. Router loopback address
B. Router IP address
C. Router priority
D. Router tracking number
200-125 exam Correct Answer: C
QUESTION 37
In which two formats can the IPv6 address fd15:0db8:0000:0000:0700:0003:400F:572B be written? (Choose two.)
A. fd15:0db8:0000:0000:700:3:400F:527B
B. fd15::db8::700:3:400F:527B
C. fd15:db8:0::700:3:4F:527B
D. fd15:0db8::7:3:4F:527B
E. fd15:db8::700:3:400F:572B
Correct Answer: AE
QUESTION 38
Which command can you enter to route all traffic that is destined for 192.168.0.0/20 to a specific interface?
A. router(config)#ip route 192.168.0.0 255.255.240.0 GigabitEthernet0/1
B. router(config)#ip route 0.0.0.0 255.255.255.0 GigabitEthernet0/1
C. router(config)#ip route 0.0.0.0 0.0.0.0 GigabitEthernet0/1
D. router(config)#ip route 192.168.0.0 255.255.255.0 GigabitEthernet0/1
200-125 dumps Correct Answer: A
QUESTION 39
Which statement about QoS default behavior is true?
A. Ports are untrusted by default.
B. VoIP traffic is passed without being tagged.
C. Video traffic is passed with a well-known DSCP value of 46.
D. Packets are classified internally with an environment.
E. Packets that arrive with a tag are untagged at the edge of an administrative domain.
Correct Answer: E
QUESTION 40
A security administrator wants to profile endpoints and gain visibility into attempted authentications. Which 802.1x mode allows these actions?
A. Monitor mode
B. High-Security mode
C. Low-impact mode
D. Closed mode
200-125 pdf Correct Answer: A
QUESTION 41
What port scanning method involves sending spoofed packets to a target system and then looking for adjustments to the IPID on a zombie system?
A. Blind Port Scanning
B. Idle Scanning
C. Bounce Scanning
D. Stealth Scanning
E. UDP Scanning
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
from NMAP:-sI <zombie host[:probeport]> Idlescan: This advanced scan method allows fora truly blind TCP port scan of the target (meaning no packets are sent tothe tar- get from your real IP address). Instead, a unique side-channelattack exploits predictable “IP fragmentation ID” sequence generation onthe zombie host to glean information about the open ports on the target.
QUESTION 42
What port scanning method is the most reliable but also the most detectable?
A. Null Scanning
B. Connect Scanning
C. ICMP Scanning
D. Idlescan Scanning
E. Half Scanning
F. Verbose Scanning
200-125 vce Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
A TCP Connect scan, named after the Unix connect() system call is the most accurate scanning method. If a port is open the operating system completes the TCP three-way handshake, and the port scanner immediately closes the connection.
QUESTION 43
What does an ICMP (Code 13) message normally indicates?
A. It indicates that the destination host is unreachable
B. It indicates to the host that the datagram which triggered the source quench message will need to be re-sent
C. It indicates that the packet has been administratively dropped in transit
D. It is a request to the host to cut back the rate at which it is sending traffic to the Internet destination
Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
CODE 13 and type 3 is destination unreachable due to communication administratively prohibited by filtering hence maybe they meant “code 13”, therefore would be C). Note:A – Type 3B – Type 4C – Type 3 Code 13D – Typ4 4
QUESTION 44
Because UDP is a connectionless protocol: (Select 2)
A. UDP recvfrom() and write() scanning will yield reliable results
B. It can only be used for Connect scans
C. It can only be used for SYN scans
D. There is no guarantee that the UDP packets will arrive at their destination
E. ICMP port unreachable messages may not be returned successfully
200-125 exam Correct Answer: DE
Explanation
Explanation/Reference:
Explanation:
Neither UDP packets, nor the ICMP errors are guaranteed to arrive, so UDP scanners must also implement retransmission of packets that appear to be lost (or you will get a bunch of false positives).
QUESTION 45
You are scanning into the target network for the first time. You find very few conventional ports open. When you attempt to perform traditional service identification
by connecting to the open ports, it yields either unreliable or no results. You are unsure of what protocols are being used. You need to discover as many different
protocols as possible. Which kind of scan would you use to do this?
A. Nmap with the sO (Raw IP packets) switch
B. Nessus scan with TCP based pings
C. Nmap scan with the sP (Ping scan) switch
D. Netcat scan with the u e switches
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
Running Nmap with the sO switch will do a IP Protocol Scan. The IP protocol scan is a bit different than the other nmap scans. The IP protocol scan is searching
for additional IP protocols in use by the remote station, such as ICMP, TCP, and UDP. If a router is scanned, additional IP protocols such as EGP or IGP may be
identified.
QUESTION 46 What ICMP message types are used by the ping command?
A. Timestamp request (13) and timestamp reply (14)
B. Echo request (8) and Echo reply (0)
C. Echo request (0) and Echo reply (1)
D. Ping request (1) and Ping reply (2)
200-125 dumps Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
ICMP Type 0 = Echo Reply, ICMP Type 8 = Echo
QUESTION 47
Which of the following systems would not respond correctly to an nmap XMAS scan?
A. Windows 2000 Server running IIS 5
B. Any Solaris version running SAMBA Server
C. Any version of IRIX
D. RedHat Linux 8.0 running Apache Web Server
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
When running a XMAS Scan, if a RST packet is received, the port is considered closed, while no response means it is open|filtered. The big downside is that not
all systems follow RFC 793 to the letter. A number of systems send RST responses to the probes regardless of whether the port is open or not. This causes all of
the ports to be labeled closed. Major operating systems that do this are Microsoft Windows, many Cisco devices, BSDI, and IBM OS/400.
QUESTION 48
home/root # traceroute www.targetcorp.com <http://www.targetcorp.com> traceroute to www.targetcorp.com <http://www.targetcorp.com> (192.168.12.18), 64 hops may, 40 byte packets 1 router.anon.com (192.13.212.254) 1.373 ms 1.123 ms 1.280 ms 2 192.13.133.121 (192.13.133.121) 3.680 ms 3.506 ms 4.583 ms 3 firewall.anon.com (192.13.192.17) 127.189 ms 257.404 ms 208.484 ms 4 anon-gw.anon.com (192.93.144.89) 471.68 ms 376.875 ms 228.286 ms 5 fe5-0.lin.isp.com
(192.162.231.225) 2.961 ms 3.852 ms 2.974 ms 6 fe0-0.lon0.isp.com (192.162.231.234) 3.979 ms 3.243 ms 4.370 ms 7 192.13.133.5 (192.13.133.5) 11.454 ms 4.221 ms 3.333 ms 6 * * * 7 * * *8 www.targetcorp.com <http://www.targetcorp.com> (192.168.12.18) 5.392 ms 3.348 ms 3.199 ms Use the traceroute results shown above to answer the following question: The perimeter security at targetcorp.com does not permit ICMP TTL-expired packets out.
A. True
B. False
200-125 pdf Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
As seen in the exhibit there is 2 registrations with timeout, this tells us that the firewall filters packets where the TTL has reached 0, when you continue with higher starting values for TTL you will get an answer from the target of the traceroute.
QUESTION 49
While attempting to discover the remote operating system on the target computer, you receive the following results from an nmap scan: Starting nmap V. 3.10ALPHA9 ( www.insecure.org/nmap/<http://www.insecure.org/nmap/> ) Interesting ports on 172.121.12.222: (The 1592 ports scanned but not shown below are in state: filtered) Port State Service
21/tcp open ftp
25/tcp open smtp
53/tcp closed domain
80/tcp open http
443/tcp open https
Remote operating system guess: Too many signatures match to reliably guess the OS. Nmap run completed — 1 IP address (1 host up) scanned in 277.483 seconds What should be your next step to identify the OS?
A. Perform a firewalk with that system as the target IP
B. Perform a tcp traceroute to the system using port 53
C. Run an nmap scan with the -v-v option to give a better output
D. Connect to the active services and review the banner information
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Most people don’t care about changing the banners presented by applications listening to open ports and therefore you should get fairly accurate information when
grabbing banners from open ports with, for example, a telnet application.
QUESTION 50
When Nmap performs a ping sweep, which of the following sets of requests does it send to the target device?
A. ICMP ECHO_REQUEST & TCP SYN
B. ICMP ECHO_REQUEST & TCP ACK
C. ICMP ECHO_REPLY & TFP RST
D. ICMP ECHO_REPLY & TCP FIN
200-125 vce Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
The default behavior of NMAP is to do both an ICMP ping sweep (the usual kind of ping) and a TCP port 80 ACK ping sweep. If an admin is logging these this will be fairly characteristic of NMAP.
See What Our Customers Are Saying:
We at Pass4itsure are committed to our customer’s success. There are 50,000+ customers who used this preparation material for the preparation of various certification exams and this number of customers is enough for new candidates to trust in these products.Our Cisco 200-125 dumps are created with utmost care and professionalism. We utilize the experience and knowledge of a team of industry professionals from leading organizations all over the world.
More individuals has download CCNA Routing and Switching 200-125 dumps study guide.”CCNA Cisco Certified Network Associate CCNA (v3.0)”, also known as 200-125 exam, is a Cisco certification which covers all the knowledge points of the real Cisco exam. Pass4itsure CCNA Routing and Switching 200-125 dumps is excellent and favored currently. Pass4itsure Cisco 200-125 dumps exam questions answers are updated (755 Q&As) are verified by experts. Great reviews have actually been given up the CCNA Routing and Switching 200-125 exam. The associated certifications of 200-125 dumps is CCNA Routing and Switching. This websites is really useful and also certainly add to our knowledge after reading it. If you like Pass4itsure CCNA Routing and Switching https://www.pass4itsure.com/200-125.html dumps, kindly share this url in your social media.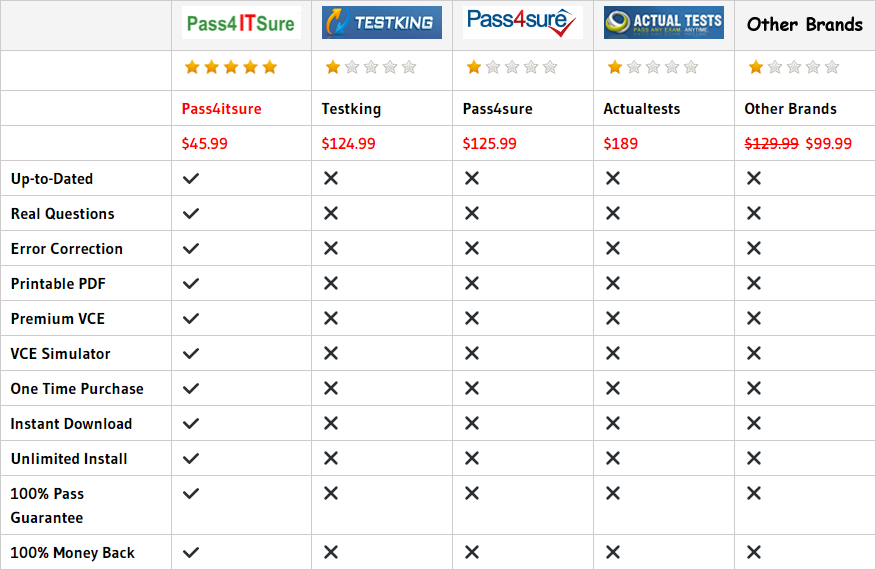
Compared with other brands, Pass4itsure has up to dated exam information, affordable price, instant exam PDF files downloadable, error correction, unlimited install,etc. Such as Pass4itsure Cisco 200-125 Dumps Real Exam Questions And Answers, Provide Discount Cisco 200-125 Dumps Certification Material Will Be More Popular, We Help You Pass CCNA Cisco Certified Network Associate CCNA (v3.0). Simple and Easy! To take advantage of the guarantee, simply contact Customer Support, requesting the exam you would like to claim. Pass4itsure guarantee insures your success otherwise get your MONEYBACK!